In my previous article I was going through the point that make a common man to understand the scenario of putting two antiviruses on the same system. But in the end I did not conclude just one antivirus is enough to protect your Industrial applications and assets, neither two antivirus engines.
Here is why.
Tuesday 7 March 2017, WikiLeaks begins its new series of leaks on the U.S. Central Intelligence Agency. Code-named “Vault 7” by WikiLeaks, it is the largest ever publication of confidential documents on the agency.
And what is it all about?
It appears to have been documents and tools circulated among former U.S. government professionals and contractors in an unauthorized manner, one of whom has provided WikiLeaks with portions of the archive. It is said to be so, no one knows, how it came out. And if someone is smart enough to get onto those networks probably they know how to keep their identities.
Now coming to the point These documents contains information about the tools they developed in-house, like an arsenal of intrusion tools that are ready to exploit any zero-day vulnerabilities.
In plain English, if you have a software in your system. Someone finds a vulnerability in that particular version. He has two choices, either to exploit the vulnerability or report to the vendor for some remunerations/incentives (of course, you can bargain). Now imagine the vulnerabilities are exploitable if the details of the vulnerabilities are out in public. The vendors of the application have to fix this immediately. And the time they may get is absolutely zero to fix this before it gets know to public and everyone start misusing it. A zero-day attack is also sometimes defined as an attack that takes advantage of a security vulnerability on the same day that the vulnerability becomes generally known.
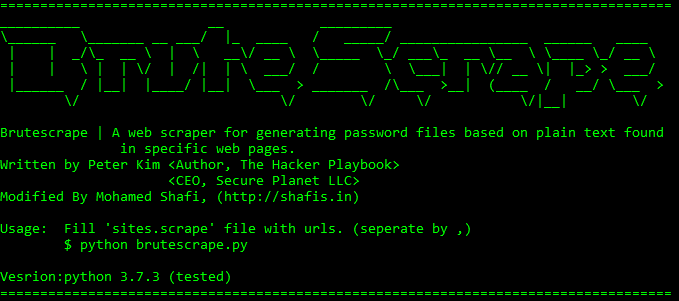
So basically, if you didn’t know this in time and take necessary action on time. You are in trouble and every single minutes counts. In plain English the tool which I mentioned above is nothing but binaries and software’s which will be uploaded in your vulnerable systems bit by bit to get the job done.
“Year Zero” introduces the scope and direction of the CIA’s global covert hacking program, its malware arsenal and dozens of “zero day” weaponized exploits against a wide range of U.S. and European company products, include Apple’s iPhone, Google’s Android and Microsoft’s Windows and even Samsung TVs, which are turned into covert microphones.
Once a single cyber ‘weapon’ is ‘loose’ it can spread around the world in seconds, to be used by rival states, cyber mafia and teenage hackers alike. If an attacker learns about this, it won’t change anything since the attacker won’t be interested in the destroying it; however, they will be interested in exploiting it and looting it. So if nothing breaks down you are happy and attacker is also happy.
Vault 7 data, dumped on March 6, 2017 by WikiLeaks, is a document detailing bypass techniques for 21 security software products. The list covers almost all major antivirus vendors, including Comodo, Avast, Kaspersky, AVG, ESET, Symantec, and others. Unfortunately, the subdirectories were missing. It is assumed that these bypass techniques are well documented and kept updated by these agencies. That means we cannot even depend upon a single antivirus. We have to have multiple antivirus running in separate physical machines. So it is always recommended to use more than one antivirus engines (installed in different PC). We don’t know who is the first one who may update virus definitions in minutes after outbreak.
With the rise in technology and development platforms, I would like to say “virus and antivirus” is old school. Sending a executable code to one system and waiting it to respond back is kind of hopeless wait. People have gone smarter. I believe we are now seeing new trends in exploiting known and unknown vulnerabilities of the applications which you are using on daily basis.
Let’s take a simple example, the questions you need to ask yourself are …
- Do you know that majority of the industrial application uses Unix / Linux Kernel with MySQL as Backend DB?
- Did you know that there was a major vulnerability in MySQL versions up to 5.1.61, 5.2.11, 5.3.5, 5.5.22 that they are so vulnerable that anyone who knows any username can get administrator access if he tries any password with approximate attempts of 300? (CVE-2012-2122)
- Do you know that you have your industrial application system that is commissioned a decade ago have MySQL database and you are still running with that?
Mohamed Shafi.